Merkle Hash Chain Audit Logs: When You Actually Need Tamper-Proof Logging
A practical guide to Merkle hash chain audit logs — what they are, how they work, and the honest question most teams skip: do you actually need one?

Your Audit Log Is Just a Database Table
You have an audit_events table. Every user action gets an INSERT. There’s a timestamp, a user ID, an action type, maybe a JSON payload. Your compliance team is happy. Your security team signs off.
But here’s a question nobody asks during the review: what stops someone with database access from quietly editing a row?
A DBA. A compromised admin account. A rogue migration script. An attacker who got past your perimeter and landed on the database. They DELETE a row, UPDATE a timestamp, INSERT a backdated entry — and your audit log, the one system that’s supposed to be the source of truth, tells a story that never happened.
Most teams don’t think about this because most teams don’t need to. But some do. And for those teams, there’s a cryptographic structure that’s been quietly solving this problem for decades.
Two Primitives, One Goal
A Merkle hash chain audit log combines two ideas. They’re often conflated, but they do different things.
Hash Chains: Sequential Integrity
A hash chain is simple. Each new log entry includes the cryptographic hash of the previous entry.
Entry 1: hash(data_1)
Entry 2: hash(data_2 + hash_of_entry_1)
Entry 3: hash(data_3 + hash_of_entry_2)If someone modifies Entry 1, its hash changes. That breaks Entry 2’s hash, which breaks Entry 3’s, which breaks everything after it. The chain becomes visibly corrupted.
This gives you append-only guarantees. You can prove that no past record was altered without checking every single entry — just verify the chain from any point forward.
Merkle Trees: Efficient Verification
Hash chains have a scaling problem. To prove that a specific entry exists and hasn’t been tampered with, you need to walk the entire chain from that point to the end. For a log with a million entries, that’s a million hash computations.
A Merkle tree fixes this. Log entries are grouped and arranged into a binary tree of hashes. The root hash — the Merkle root — is a single fingerprint that represents every entry in the tree.
The key property: to prove any single entry belongs to the tree, you only need log₂(n) hashes. For a million entries, that’s about 20 hashes instead of a million. This is called an inclusion proof or Merkle proof.
Root Hash
/ \
Hash(AB) Hash(CD)
/ \ / \
Hash(A) Hash(B) Hash(C) Hash(D)
| | | |
Entry1 Entry2 Entry3 Entry4An auditor receives the sibling hashes along the path from the entry to the root. They recompute upward and check if the result matches the published root. If it does, the entry is authentic. If it doesn’t, something was tampered with.
Think of hash chains as a tamper-evident seal on the sequence of events, and Merkle trees as an efficient index for verifying individual events. Real-world systems use both together — the chain ensures ordering, the tree enables fast proofs.
How It Works in Practice
Here’s a minimal Go implementation to make this concrete:
package auditlog
import (
"crypto/sha256"
"encoding/hex"
"fmt"
"time"
)
type Entry struct {
Sequence uint64
Timestamp time.Time
Action string
Data []byte
PrevHash string // hash chain link
Hash string
}
func NewEntry(prev *Entry, action string, data []byte) Entry {
e := Entry{
Timestamp: time.Now().UTC(),
Action: action,
Data: data,
}
if prev != nil {
e.Sequence = prev.Sequence + 1
e.PrevHash = prev.Hash
}
// Hash includes the previous hash, creating the chain
payload := fmt.Sprintf("%d|%s|%s|%s|%x",
e.Sequence, e.Timestamp.Format(time.RFC3339Nano),
e.Action, e.PrevHash, e.Data,
)
sum := sha256.Sum256([]byte(payload))
e.Hash = hex.EncodeToString(sum[:])
return e
}Each entry hashes its own content plus the previous entry’s hash. Modify any entry and the chain breaks from that point forward.
This example uses a simple |-delimited string for hashing. In production, you’d want length-prefixed fields or a canonical serialization format (like Protocol Buffers or CBOR) to prevent field boundary confusion — where a crafted Action value containing | could produce the same hash payload as a different entry.
For the Merkle tree layer, entries are periodically grouped into blocks. Each block computes a Merkle root over its entries. The root gets published — to a separate datastore, a public ledger, or even printed and mailed to an auditor. This is called anchoring.
The Real Question: Do You Actually Need This?
This is where most articles on Merkle trees stop — at the “how.” But the more important question is “should you.”
Here’s the honest assessment.
You Need Tamper-Evident Logging When
Regulatory compliance demands provable integrity. Financial services under SEC Rule 17a-4 need to demonstrate that trade records haven’t been altered. Healthcare systems under HIPAA need audit trails that can withstand legal scrutiny. If a regulator can ask “prove this record wasn’t changed” and your answer is “trust us, we have access controls,” you have a problem.
Multiple parties with conflicting interests share a log. When a vendor and a customer both need to trust the same event history, neither party should be able to unilaterally rewrite it. Merkle-anchored logs with published roots give both parties independent verification.
The consequences of undetected tampering are severe. Certificate Transparency — arguably the most successful deployment of this pattern — exists because a single rogue SSL certificate can compromise the security of millions of users. The log doesn’t prevent issuance of bad certificates. It makes them detectable.
Your threat model explicitly includes insider access. If you’re worried about a compromised DBA or a malicious admin modifying records, access controls alone aren’t enough. You need a system where tampering leaves a cryptographic trace that the tamperer can’t clean up.
You Don’t Need It When
Your threat model doesn’t include database-level access. If the realistic threats to your audit log are application bugs and misconfigured permissions — not a sophisticated attacker with direct database access — a standard append-only table with proper access controls is fine. Add a deleted_at IS NULL constraint and call it a day.
You control the entire stack and trust your operators. Internal tool for a small team? The operational overhead of maintaining hash chains, anchoring Merkle roots, and building verification tooling isn’t justified by the threat you’re defending against.
You’re doing it because it sounds cool. I’ve seen teams add Merkle trees to their logging pipeline because they read about it in a blockchain article. Their actual audit requirement was “keep logs for 90 days.” A properly configured S3 bucket with Object Lock would have taken an afternoon instead of a sprint.
Adding cryptographic integrity to your audit log introduces real operational complexity: key management for signing roots, verification tooling for auditors, a process for handling detected inconsistencies, and a separate anchoring system that the log operator doesn’t control. If you don’t have a clear threat that justifies this complexity, you’re adding attack surface, not reducing it.
The Decision Framework
Before reaching for a Merkle hash chain, answer these three questions:
1. Who are you defending against?
If the answer is “external attackers who might compromise the application layer” — standard logging with immutable storage (S3 Object Lock, WORM storage, append-only database permissions) is probably sufficient. The attacker can’t modify what they can’t access.
If the answer includes “insiders, operators, or anyone with infrastructure access” — you need cryptographic integrity. Access controls protect against unauthorized access. Hash chains protect against authorized access being misused.
2. Who needs to verify the log?
If verification is internal-only, you can use simpler schemes. A nightly job that recomputes hashes and alerts on mismatches might be all you need.
If external parties need to independently verify entries without trusting your infrastructure, you need Merkle proofs and published roots. This is the Certificate Transparency model — anyone can verify, no one needs to trust the log operator.
3. What’s the cost of undetected tampering?
If someone modifies your internal feature-flag audit log and nobody notices, the consequence is confusion in a debugging session. If someone modifies a financial transaction log and nobody notices, the consequence is fraud, regulatory penalties, and criminal liability.
Scale your integrity guarantees to match the stakes.
Real-World Deployments Worth Studying
Certificate Transparency is the gold standard. Every publicly trusted TLS certificate must include Signed Certificate Timestamps (SCTs) from at least two CT logs. Browsers verify inclusion proofs. This system has caught misissued certificates from major CAs that would have otherwise gone undetected.
Amazon QLDB used an internal Merkle-based journal as its core data structure. Every change was appended to an immutable, cryptographically verifiable log. AWS shut it down entirely in July 2025, recommending migration to Aurora PostgreSQL — a reminder that even managed solutions for this pattern can disappear, and understanding the underlying primitives matters.
The most effective deployment of Merkle-based audit logging isn’t the one with the most sophisticated tree structure. It’s the one where the Merkle root gets published somewhere the log operator can’t reach — a third-party timestamp service, a separate organization’s infrastructure, or a public append-only ledger. The root is meaningless if the same party controls both the log and the anchor.
The Anchoring Problem Most People Skip
Building the hash chain is the easy part. The hard part is anchoring — publishing the Merkle root somewhere tamper-proof and independent.
Options, in order of increasing trust guarantees:
- Separate database with different access controls — Minimal. Stops casual tampering, not a determined insider.
- Object storage with WORM/Object Lock — Better. The cloud provider guarantees immutability for the retention period.
- Third-party timestamp authority (RFC 3161) — Strong. A trusted third party attests that the root existed at a specific time. Used in legal contexts.
- Public append-only ledgers — Strongest for multi-party verification. Certificate Transparency logs, blockchain-based anchoring.
The level of anchoring you need maps directly back to your threat model. Don’t anchor to a public blockchain if a WORM S3 bucket meets your requirements. Don’t use a WORM S3 bucket if your threat model includes a compromised AWS account.
Where This Actually Matters Next
Two emerging areas are pushing Merkle audit logs from niche to necessary.
AI agent accountability. As autonomous agents take actions on behalf of users — making purchases, modifying infrastructure, sending communications — the question “what exactly did the agent do, and can we prove the log wasn’t edited after the fact?” becomes critical. A hash-chained decision log with anchored Merkle roots is the difference between “the agent says it did X” and “we can cryptographically prove the agent did X.”
Supply chain integrity. Software supply chain attacks have made it clear that knowing what went into a build isn’t enough — you need to prove nothing was added after the fact. Systems like Sigstore use Merkle-based transparency logs (Rekor) to make the provenance of software artifacts verifiable by anyone.
The Honest Takeaway
Merkle hash chain audit logs are elegant. The cryptography is sound. The guarantees are real.
But they’re a tool for a specific threat model, not a default choice. Most applications need audit logging. Very few need cryptographically tamper-evident audit logging. The difference is whether your threat model includes someone with the access and motivation to quietly rewrite history — and whether the consequences of that rewrite justify the engineering investment to prevent it.
If you can’t articulate who the attacker is, what they’d modify, and why existing access controls aren’t sufficient — you don’t need a Merkle tree. You need a well-designed append-only table and a good backup strategy.
But if you can answer those questions, and the stakes are real, this is one of the few patterns in software where the math genuinely has your back.
Other posts
See all posts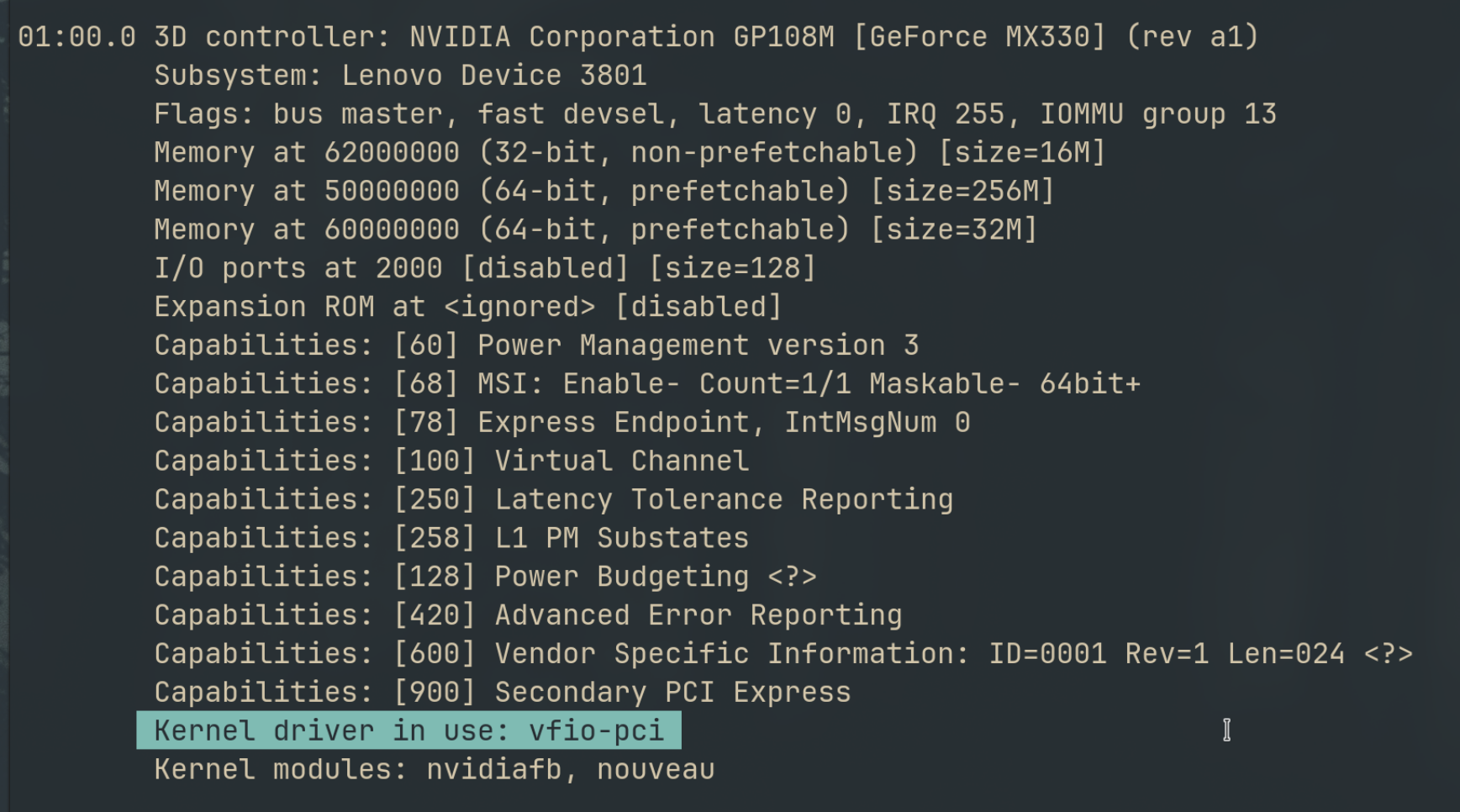
Why Your Laptop GPU Will Never Work with Proxmox Passthrough
Six attempts, three days, one stubborn MX330. A post-mortem on laptop GPU passthrough in Proxmox — what failed, why it's architecturally impossible, and exactly what to buy instead.
Your Old Laptop Is a Linux Server: A Complete Proxmox Home Lab Setup Guide
Turn an old laptop into a full Proxmox home server — Wi-Fi NAT routing, DHCP, MTU fixes, and every gotcha you'll actually hit. A practical guide that also teaches you how AWS works.
Quantum Computing for the Curious Developer: Building Your First Circuits with Qiskit
A developer's hands-on guide to quantum computing fundamentals — from qubits and gates to building a quantum teleportation circuit, no physics degree required.
